Financial institutions across multiple jurisdictions are experiencing a persistent and evolving threat: customers opening bank accounts—often through digital onboarding channels—and subsequently transferring control of those accounts to third parties who use them for fraud and money laundering. This practice, commonly referred to as money mule account provisioning or account leasing, has become a critical enabler of financial crime by providing criminal networks with access to seemingly legitimate banking relationships.
Because these accounts originate from genuine onboarding processes, they bypass many traditional fraud controls and can operate undetected long enough to facilitate significant illicit activity.
Understanding the Scheme
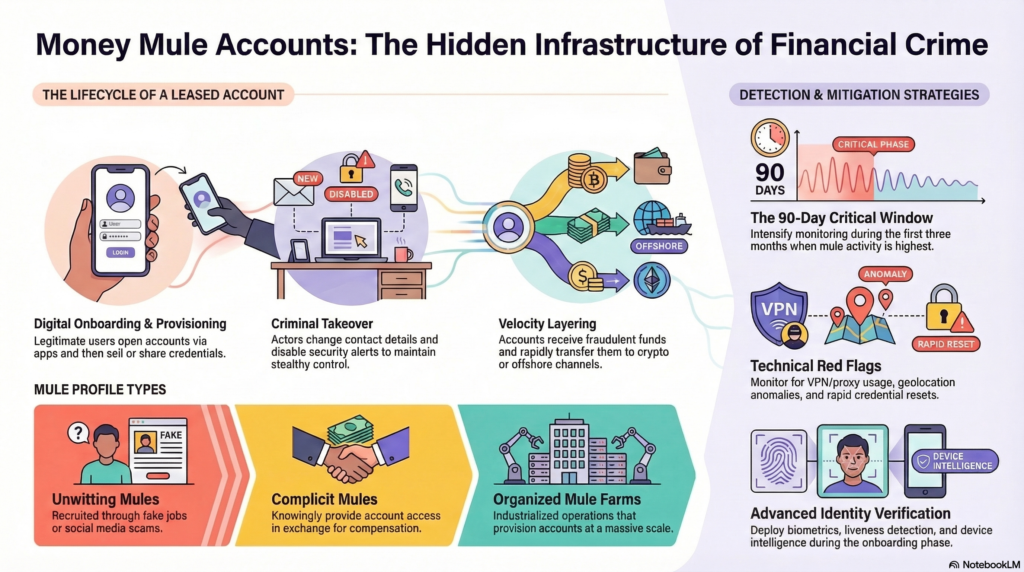
In a typical scenario:
- An individual opens a bank account, frequently via remote or app-based onboarding.
- Shortly after activation, the account holder:
- sells access credentials,
- shares authentication devices or OTP access,
- or knowingly collaborates with third parties.
- Control of the account shifts to criminal actors who:
- change contact details (phone, email),
- reset credentials and authentication factors,
- disable alerts and security notifications.
- The account is used to receive fraudulent proceeds and rapidly transfer funds onward to additional mule accounts, cryptocurrency platforms, or cash-out channels.
Subsequent access often originates from foreign jurisdictions, anonymization services, or device environments inconsistent with the original onboarding profile.
Terminology and Typologies
This activity is associated with several FinCrime classifications:
- Money mule recruitment
- Account renting / account leasing
- Drop accounts
- Collusive account takeover
- Mule account provisioning
- Facilitated mule activity
Key participant profiles include:
- Unwitting mules recruited through fake job offers or social media schemes.
- Complicit mules who knowingly provide account access for compensation.
- Account sellers who open accounts specifically for resale.
- Organized mule farms that industrialize account provisioning.
Why Criminal Networks Value Newly Opened Accounts
Fresh accounts offer several operational advantages:
- Clean transactional history and low risk scoring at inception
- Lower scrutiny during early lifecycle stages
- S쳾ufficient transaction limits to enable rapid fund movement
- Legitimate KYC credentials that increase trust within payment ecosystems
These characteristics make them ideal for the placement and layering stages of money laundering, as well as for routing proceeds from scams such as phishing, business email compromise (BEC), and authorized push payment fraud.
Watch on YouTube: Money Mule Accounts and Account Leasing
Operational Indicators and Red Flags
Onboarding Phase
- Multiple accounts opened with similar device fingerprints or emulator signatures
- Use of IP ranges associated with hosting providers, VPNs, or anonymization services
- Repeated document templates or synthetic identity indicators
- Behavioral anomalies during identity verification steps
Early Account Lifecycle (First 30–90 Days)
Customer Profile Changes
- Rapid modification of phone numbers and email addresses
- Reset of credentials shortly after onboarding
- Deactivation of alerts and communication preferences
Access and Authentication Anomalies
- Logins from geographically distant locations within short intervals
- Use of VPN, proxy, or TOR infrastructure
- Device fingerprint changes inconsistent with normal consumer behavior
Transactional Behavior
- Incoming funds from multiple unrelated senders
- Immediate outbound transfers (“velocity layering”)
- High-volume pass-through activity without typical retail spending patterns
- Rapid escalation in transaction size and frequency
Criminal Operating Models
Individual Account Resale
A single account holder sells access to one or more criminal actors.
Organized Mule Recruitment Networks
Groups recruit individuals to open accounts at scale, often targeting students, migrants, or financially vulnerable populations.
Synthetic Identity Account Provisioning
Accounts are opened using fabricated or hybrid identities and later sold.
Collusive Account Takeover
The legitimate account holder cooperates by sharing authentication codes or approving access requests.
Risk and Compliance Implications
AML/CFT Exposure
These accounts serve as conduits for laundering criminal proceeds and facilitating organized financial crime.
Fraud Enablement
Mule accounts support scams, phishing operations, and payment diversion schemes.
Regulatory Risk
Weaknesses in onboarding controls and ongoing monitoring may attract regulatory scrutiny and enforcement action.
Reputational Risk
Association with criminal fund flows can undermine institutional trust.
Mitigation Strategies
Strengthening Digital Onboarding
- Biometric verification and liveness detection
- Device intelligence and emulator detection
- Behavioral analytics during identity verification
- Cross-channel identity risk scoring
Early-Life Account Monitoring
- Enhanced monitoring during the first 30–90 days
- Risk triggers for contact detail changes
- Dynamic risk scoring based on behavioral deviation
Access and Authentication Controls
- VPN/proxy detection and risk-based authentication
- Geolocation anomaly monitoring
- Device binding and step-up verification protocols
Network and Mule Detection Analytics
- Beneficiary clustering and network linkage analysis
- Velocity and layering pattern detection
- Shared device and credential correlation
- Interbank intelligence sharing where permissible
Investigative and Enforcement Considerations
When indicators suggest collusion or intentional facilitation:
- the account holder may be classified as a complicit facilitator,
- the account may be subject to restriction, suspension, or closure,
- suspicious activity reporting obligations may be triggered,
- collaboration with law enforcement may be warranted.
Distinguishing between unwitting participation and deliberate facilitation is critical for proportional response and regulatory defensibility.
Conclusion
Money mule accounts and account leasing represent foundational infrastructure for modern financial crime. The expansion of digital onboarding has improved customer accessibility but has simultaneously lowered barriers for criminal exploitation.
Effective mitigation requires a lifecycle approach: robust onboarding controls, intensified early account monitoring, behavioral analytics, and coordinated investigative response. Financial institutions that integrate fraud prevention and AML intelligence capabilities will be best positioned to disrupt mule networks and protect the integrity of the financial system.



GIPHY App Key not set. Please check settings