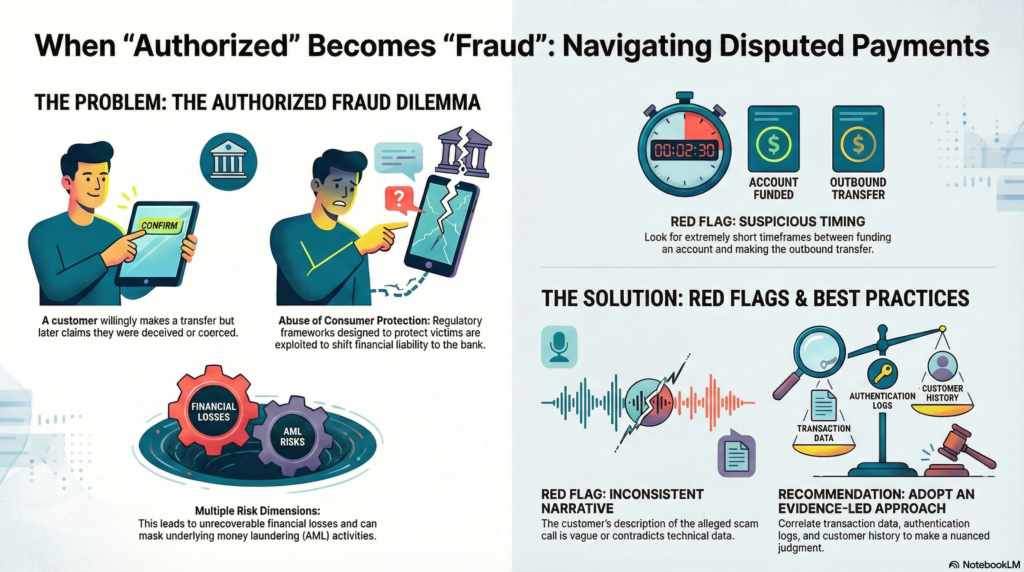
In recent years, Financial Crime (FinCrime) teams have observed a growing number of disputed payment cases that sit in a grey area between genuine fraud victimization and deliberate customer misconduct. A recurring scenario involves a customer who transfers funds—often after moving liquidity internally—and immediately forwards those funds to a third-party account. Shortly thereafter, the customer contacts the bank claiming the transfer was unauthorized, attributing the event to a phone-based scam in which the fraudster allegedly impersonated the bank itself.
This pattern presents significant challenges for fraud management, customer protection, and regulatory compliance.
The Nature of the Scheme
From a technical standpoint, these transactions are typically authorized push payments: the customer passes authentication controls and actively instructs the transfer. However, the post-transaction narrative reframes the payment as fraudulent, with the customer asserting manipulation, coercion, or deception.
While many such cases do involve genuine social engineering, FinCrime investigations increasingly identify situations where:
- the customer retains full control throughout the transaction flow,
- the beneficiary account shows signs of prior linkage or familiarity,
- or the complaint appears strategically timed to trigger reimbursement processes.
In these circumstances, the scam narrative may be exaggerated—or entirely fabricated—to shift financial liability to the bank.
Watch on YouTube: Authorized Push Payment Fraud or Customer Abuse
Key Risk Dimensions for Banks
1. Financial Loss Risk
Reimbursement of customer-authorized transactions, particularly when funds have already exited the banking perimeter, often results in unrecoverable losses.
2. Abuse of Consumer Protection Frameworks
Regulatory and internal policies designed to protect genuine victims can be exploited, especially where reimbursement standards are inconsistently applied.
3. AML and Collusion Risk
Some cases reveal indicators of collusion with money mules or third parties, raising concerns beyond fraud into anti-money laundering and facilitation of criminal activity.
4. Reputational and Conduct Risk
Incorrectly denying legitimate victims or, conversely, reimbursing abusive claims both carry reputational consequences.
Common Red Flags Observed
FinCrime teams commonly identify the following indicators in abusive or high-risk cases:
- Extremely short timeframes between internal funding and outbound transfer
- Immediate escalation to fraud claims after funds are sent
- Beneficiaries located in high-risk jurisdictions or previously unseen mule typologies
- Inconsistencies in the customer’s description of the alleged scam call
- Evidence of strong customer authentication successfully completed without anomaly
- Resistance to providing call details, phone numbers, or precise timelines
While no single factor is determinative, the aggregation of such signals materially increases suspicion of customer abuse or collusion.
Investigative and Decision-Making Considerations
Effective handling of these cases requires a structured, evidence-led approach. Best practices include:
- correlating transaction data with authentication logs and device information,
- assessing behavioral consistency with the customer’s historical profile,
- applying a clear distinction between technical authorization and psychological coercion,
- documenting decision rationales to ensure auditability and regulatory defensibility.
Importantly, FinCrime teams must avoid binary thinking. These cases rarely fall cleanly into “fraud” or “customer fault” categories and require nuanced judgment supported by robust governance.
Conclusion
Disputed transfers following customer-authorized payments represent one of the most complex challenges in modern fraud operations. The overlap between genuine social engineering, customer negligence, and deliberate abuse demands mature investigative frameworks and close collaboration between fraud, AML, legal, and customer protection functions.
As scam narratives grow more sophisticated—and as customer awareness of reimbursement mechanisms increases—banks must continue refining their detection, investigation, and adjudication capabilities to balance fairness, financial risk, and regulatory expectations.




GIPHY App Key not set. Please check settings