Insider threats are a critical financial crime risk because they arise from individuals who already possess authorized access, operational knowledge, or institutional trust and then misuse that position to cause harm. In official security guidance, an insider threat is generally understood as the potential for an insider to use authorized access or knowledge of an organization to damage it. In the financial crime environment, that harm can extend far beyond information misuse. It can include facilitation of fraud, circumvention of AML controls, inappropriate customer onboarding, suppression of alerts, misuse of customer data, sanctions evasion, bribery, collusion with criminal networks, market abuse, and concealment of suspicious activity.
From a professional financial crime perspective, insider threat is especially serious because it attacks the integrity of the control environment from within. Many financial crime frameworks are designed to identify suspicious customers, transactions, and external actors. Insider threat changes that equation by introducing the possibility that the institution’s own employees, contractors, temporary staff, agents, or other trusted persons may undermine those controls intentionally or negligently. This makes insider threat more than a conduct issue. It is a structural control risk that can compromise all three lines of defence if governance, access management, oversight, and escalation processes are weak. The FCA’s financial crime guidance is explicitly concerned with firms’ systems and controls against fraud, money laundering, bribery and corruption, and related risks, which is directly relevant to insider-enabled abuse.
In practical terms, insider threats in financial services can take several forms. At one end of the spectrum is malicious insider activity, where an individual knowingly abuses access for personal gain, retaliation, coercion, or collusion with external criminals. This may involve overriding controls, leaking customer information, manipulating records, authorizing prohibited activity, or tipping off subjects of investigations. At the other end are careless or compromised insiders whose weak security behaviour, poor judgment, or susceptibility to coercion creates openings for financial crime. Both forms matter. A deliberately corrupt employee and a negligent employee can each weaken the institution’s ability to prevent fraud and money laundering, although the control response may differ. CISA’s definition of insider threat is broad enough to encompass misuse of access and organizational knowledge in either context.
The financial crime implications are particularly acute because insiders can interfere with exactly those processes that institutions rely on to maintain trust and regulatory compliance. An insider may facilitate the onboarding of high-risk or fictitious customers, manipulate KYC records, approve exceptions without proper basis, suppress sanctions or transaction-monitoring alerts, alter payment instructions, access dormant accounts, or help criminal associates understand internal thresholds and detection logic. In more sophisticated cases, insiders may enable the placement, layering, or concealment of illicit funds by exploiting knowledge of control gaps and operational blind spots. The result is that suspicious activity may appear normal, exceptions may seem properly authorized, and red flags may never be escalated. This is an inference from the way official financial crime guidance emphasizes robust systems, controls, training, and oversight as core defenses against abuse.
Watch on YouTube: Insider Threats
One of the reasons insider threats are so difficult to manage is that authorized access creates a presumption of legitimacy. An employee with the right credentials can often perform actions that would appear suspicious if attempted by an outsider. Access to customer data, case files, payment workflows, alert queues, and internal systems is frequently necessary for legitimate job performance. The control challenge is therefore not simply restricting access, but ensuring that access is proportionate, monitored, and explainable. In the financial crime environment, this means firms need to understand not only who can do what, but also whether their actions are consistent with role, timing, business justification, and expected behavioural patterns. CISA’s insider-threat framing is directly relevant here because it focuses on harm arising from authorized access and organizational understanding.
Insider threat also intersects with wider organizational vulnerabilities such as weak segregation of duties, ineffective challenge culture, excessive privilege, poor logging, weak case oversight, and inadequate escalation channels. A financial institution may have well-written AML and fraud policies, but those policies can be neutralized if employees are able to bypass dual controls, self-approve changes, manipulate audit trails, or intimidate junior staff from escalating concerns. Regulatory guidance on financial crime systems and controls consistently emphasizes governance, accountability, documentation, and management oversight because those features help prevent control environments from becoming too dependent on individual trust. In other words, insider threat is often a symptom of broader governance weakness as much as individual misconduct.
The typology also has an important connection to organized criminal exploitation. Insiders may be recruited, bribed, pressured, or socially engineered by external actors seeking access to accounts, customer data, transaction pathways, or investigative intelligence. In some cases, the insider is fully complicit. In others, the relationship develops gradually through gifts, favors, emotional manipulation, financial distress, or coercive leverage. This creates a difficult risk-management problem because the insider may initially appear to be a normal employee whose conduct only becomes suspicious over time. A mature financial crime framework therefore needs to consider insider threat not merely as an HR or security issue, but as a possible conduit between the institution and external criminal networks. The broader regulatory focus on bribery, corruption, fraud, and money laundering control environments supports this integrated view.
A professionally mature response to insider threat begins with governance and risk assessment. Firms should explicitly consider insider-enabled abuse within enterprise risk assessments, business-wide financial crime risk assessments, fraud frameworks, and control-testing programmes. The question is not whether employees are trusted in general, but where trust creates concentrated risk. High-exposure areas may include onboarding, payments operations, transaction monitoring, sanctions screening, correspondent banking, high-risk customer servicing, investigations, market-facing desks, and privileged technology roles. The FCA has stressed the importance of firms documenting financial crime risk and ensuring systems and controls remain effective, which is directly relevant to how insider risk should be assessed and owned.
Control design in this area must be layered. Access should be role-based and limited to what is genuinely necessary. Sensitive actions should require segregation of duties, dual approval, or independent review where appropriate. Staff in higher-risk roles should be subject to enhanced supervision, stronger quality assurance, and more robust activity logging. Customer and case-data access should be monitored for unusual patterns, such as access outside normal job function, repetitive review of unrelated accounts, inappropriate downloads, excessive overrides, or intervention in cases without a clear business rationale. These are logical implications of the insider-threat principle that authorized access must still be monitored for harmful misuse.
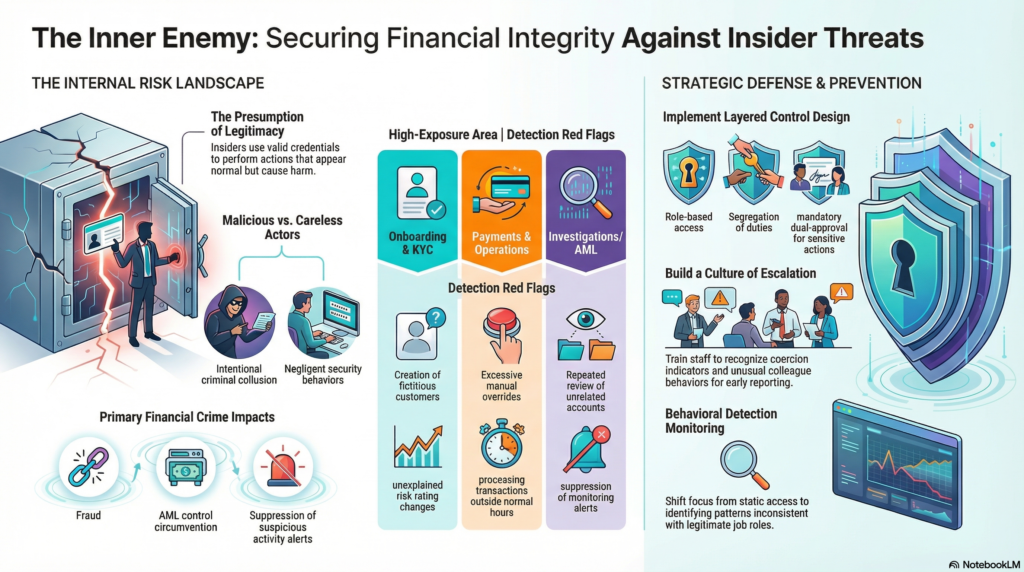
Training and culture are equally important. Firms need employees to understand not only confidentiality and conduct obligations, but also how insider-enabled financial crime can occur and how concerns should be escalated. This includes awareness of bribery risk, conflicts of interest, coercion indicators, unusual colleague behaviour, inappropriate requests for system access, and attempts to obtain information outside normal need-to-know boundaries. A strong culture of escalation is essential because insider threat is often detected through human concern as much as through technical controls. Regulatory emphasis on effective systems and controls implicitly depends on staff being willing and able to raise issues before harm escalates.
Detection capability should also be treated as a core requirement. In financial crime terms, insider threat monitoring may include review of unusual access to customer files, override activity, exceptional approval patterns, unexplained changes to customer risk ratings, suspicious suppression of alerts, atypical after-hours activity, case-handling anomalies, and interactions between employee activity and suspicious transaction flows. The objective is not to create indiscriminate surveillance, but to identify patterns that are inconsistent with legitimate role performance. Because money laundering and fraud processes are often handled by different teams, institutions also need to ensure that intelligence is joined up; FinCEN has noted that fraud-related and money-laundering-related suspicious activity are often interconnected even when investigated separately.
Operational response must be disciplined once insider threat is suspected. The institution may need to secure access, preserve evidence, review affected accounts or cases, assess whether suspicious activity reporting obligations are engaged, and determine whether customers, counterparties, or regulators may have been impacted. Investigations should examine not only the individual’s conduct, but also whether similar control weaknesses could be exploited elsewhere. In a financial crime setting, an insider incident may have implications for KYC integrity, sanctions controls, transaction monitoring reliability, fraud losses, and the defensibility of prior decisions. That means remediation often extends beyond disciplinary action to wider control redesign and assurance work. This is an inference supported by the regulatory focus on systems, controls, and documented risk management.
Ultimately, insider threats are a serious financial crime risk because they allow harm to be carried out from within the trusted perimeter of the institution. They can weaken fraud defenses, compromise AML controls, expose customer data, facilitate illicit payments, and undermine the credibility of governance and assurance functions. In a modern financial services environment, firms cannot rely solely on trust in personnel or static access controls. They need a structured framework that treats insider threat as part of the broader financial crime ecosystem, with clear ownership, proportionate monitoring, strong challenge, and coordinated response across compliance, fraud, AML, security, operations, HR, and senior management. Only then can insider risk be managed as the control-critical issue it truly is.