The Automated Clearing House, or ACH, is a U.S. electronic payments network that enables depository institutions to send and receive batches of electronic credit and debit transfers. The Federal Reserve describes ACH as a nationwide network for batched electronic credit and debit transfers, while Nacha describes the ACH Network as a batch-oriented electronic funds transfer system governed by the Nacha Operating Rules. ACH supports a wide range of routine payment activity, including payroll direct deposits, tax refunds, bill payments, mortgage debits, business disbursements, and other recurring or one-time account-to-account transfers.
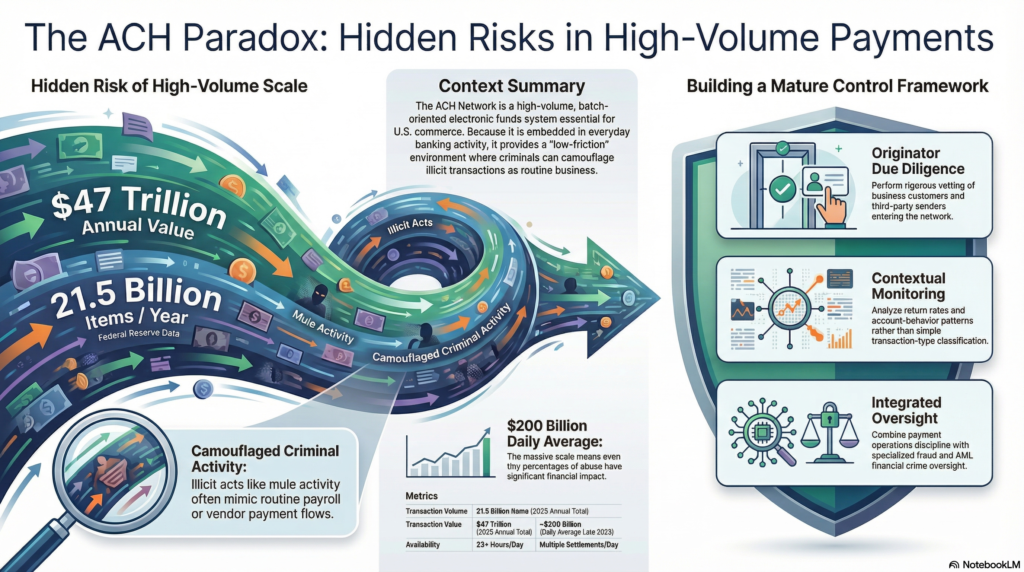
In the financial crime environment, ACH is significant because it combines high volume, broad reach, and comparatively low friction with access to ordinary retail and commercial bank accounts. Those characteristics make it commercially essential, but they also make it attractive for misuse. Financial institutions can use ACH to move legitimate payments efficiently across the banking system, yet criminals can also attempt to exploit the same infrastructure for fraud, account abuse, business email compromise proceeds, mule-account activity, unauthorized debits, and the movement of illicit funds through accounts that appear routine. The financial crime challenge is therefore not the existence of ACH itself, but the fact that it is embedded in everyday banking activity and can be abused without looking unusual at first glance.
A professionally mature understanding of ACH begins with its operational model. ACH payments are generally batch-based rather than instant, although Nacha notes that the network supports both standard ACH and Same Day ACH processing. Nacha states that the ACH Network processes payments more than 23 hours each banking day and settles them multiple times per banking day, while the Federal Reserve notes that commercial ACH services support same-day and next-day settlement options. This means ACH sits in an important middle ground within the payment ecosystem: it is faster and more automated than legacy paper-based methods, but it is not the same as instant-payment rails. That timing difference matters in financial crime terms because it affects detection windows, return processes, and opportunities for intervention.
From a financial crime perspective, ACH risk can arise on both the credit and debit side of the network. ACH credits can be used to move funds into accounts that are later used for layering, pass-through activity, or fraud proceeds collection. ACH debits create additional exposure because they may involve unauthorized pulls from consumer or business accounts if account information is compromised or if originators misuse authorization processes. This makes ACH relevant not only to AML controls, but also to fraud prevention, authentication, account integrity, and originator due diligence. Nacha’s rules framework and authentication guidance reflect this by placing obligations on participating institutions and emphasizing commercially reasonable authentication, particularly for certain internet-initiated entries.
Watch on YouTube: Automated Clearing House (ACH)
One of the key financial crime risks in ACH is that abusive activity can be embedded inside apparently routine payment flows. Payroll files, vendor payments, recurring debits, and consumer bill payments are ordinary features of the network, which means suspicious activity may not present with the obvious novelty often seen in more visibly anomalous transactions. A mule account receiving ACH credits from multiple unrelated sources, for example, may initially appear to be receiving ordinary account-to-account transfers. Likewise, an unauthorized debit scheme may resemble legitimate billing behavior unless authorization quality, return patterns, and originator conduct are reviewed carefully. This is why ACH risk management depends heavily on contextual monitoring rather than simple payment-type classification. The inference here is supported by the ACH network’s role in ordinary recurring and batch payments and by the rules-based responsibilities imposed on participating institutions.
The role of governance is especially important because ACH is not an unstructured payment channel. Nacha states that the Operating Rules define the roles and responsibilities of ACH Network participants and are foundational for every ACH payment. This means ACH risk should be managed not only through generic financial crime policies, but also through network-specific rules, originator oversight, return monitoring, authentication standards, and compliance obligations. In practical terms, financial institutions need to understand who is originating ACH activity, under what authority, for what purpose, with what expected pattern, and subject to what contractual and operational controls.
For firms operating in the ACH environment, originator risk is often one of the most important control areas. A bank or credit union may not itself be the commercial actor initiating the underlying transactions, but it is still part of the chain through which those payments enter the network. That means due diligence over business customers, third-party senders, payment processors, and service providers is critical. Nacha’s materials on third parties make clear that third-party service providers and other participants have defined compliance obligations, including audit obligations for ACH processing functions they perform. In financial crime terms, this reinforces that ACH exposure is not limited to the end transaction; it also includes the quality of control over the participants introducing activity into the network.
ACH is also relevant to AML because the network can be used to move value through ordinary deposit accounts in ways that may support layering or concealment. While ACH is not usually the most opaque payment channel, its ubiquity and legitimate business use can make suspicious movement harder to isolate if institutions do not compare transaction behavior against expected account purpose and customer profile. A commercial account receiving repeated ACH credits and rapidly pushing funds onward, or a retail account receiving business-like ACH activity from unrelated entities, may indicate fraud proceeds, mule use, or other forms of misuse. In this sense, ACH monitoring should be integrated into broader transaction-monitoring and customer-risk frameworks rather than treated as a standalone payment operations issue. This is an inference drawn from the ACH network’s broad use for account-to-account transfers and the operational structure described by the Federal Reserve and Nacha.
A mature control framework for ACH therefore combines payment operations discipline with financial crime oversight. This includes originator due diligence, authorization controls, return-rate and exception monitoring, account-behavior analysis, customer risk-rating, sanctions and screening controls where relevant, and escalation pathways for suspicious ACH activity. It also requires strong data quality and visibility across parties, because ACH misuse may become apparent only when multiple payments, counterparties, or return events are viewed together. Firms that treat ACH solely as a settlement utility may miss the wider fraud and AML implications of the activity moving through it.
There is also an important scale dimension. Federal Reserve data show that the ACH system continues to process very large volumes and values of transactions. In 2025, Federal Reserve commercial ACH transactions totaled more than 21.5 billion items and more than $47 trillion in value, with quarterly figures in late 2025 showing average daily values near $200 billion. Those numbers illustrate why ACH deserves attention in the financial crime environment: even a small percentage of abusive activity can have significant operational and financial impact when embedded in a network of this size.
Ultimately, ACH is a core payments infrastructure in the U.S. financial system, but in financial crime terms it is also a channel that can be exploited for fraud, unauthorized debits, mule-account activity, and the movement of suspicious funds. Its routine nature is part of both its value and its risk. Because ACH payments often look ordinary, institutions need controls that go beyond simple payment processing and address the identity, authority, behavior, and purpose behind the transactions. For that reason, ACH should be understood not merely as a payments rail, but as a critical area of financial crime control requiring integrated oversight across payments operations, fraud, AML, compliance, and governance.




