Anti-Money Laundering software is the set of technological tools, platforms, and data-processing capabilities used by financial institutions to identify, assess, monitor, investigate, and report money laundering risk. In the financial crime environment, AML software is not a standalone control and it is not a substitute for judgment, governance, or regulatory accountability. It is best understood as an operational layer within the broader AML framework, supporting how firms apply customer due diligence, transaction monitoring, sanctions screening, case management, and suspicious activity escalation in a consistent and scalable way. Regulators and standard-setters continue to emphasize that AML controls must be risk-based, proportionate, and effective, and that technology can strengthen those outcomes when properly governed.
In practice, AML software exists because modern financial institutions cannot manage financial crime risk manually at the scale, speed, and complexity of contemporary payment and customer environments. Firms process large volumes of transactions across multiple products, geographies, customer types, and channels, often in near real time. They must also maintain oversight of onboarding risk, beneficial ownership, sanctions exposure, and unusual account behavior throughout the customer lifecycle. FATF has noted both the opportunities and challenges created by new technologies for AML/CFT, including the need to process data at speed and scale, while the FCA has recently updated guidance around transaction monitoring and responsible innovation within financial crime systems and controls.
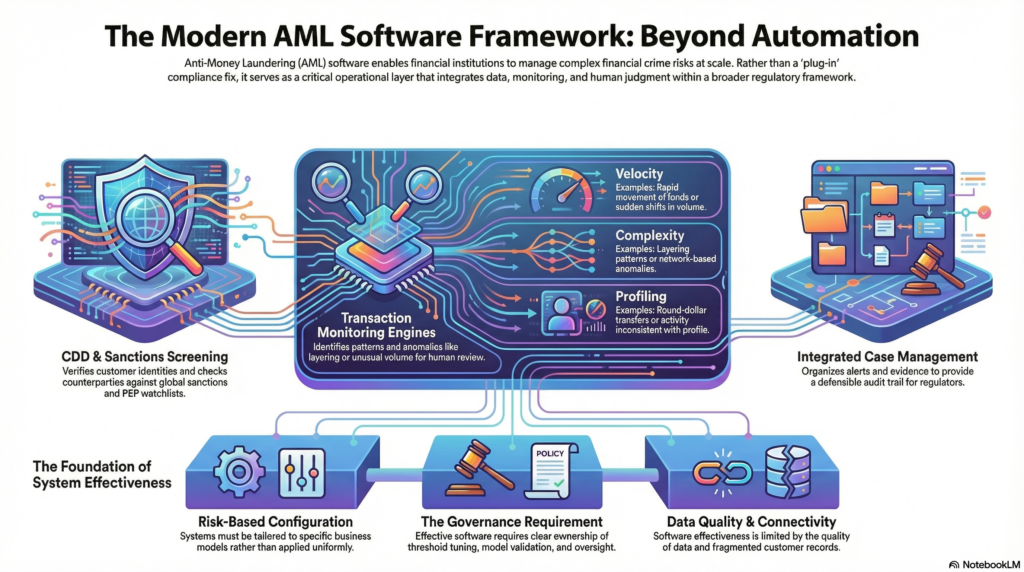
A professionally mature AML software environment usually consists of several core functional components. Customer due diligence tools support identity verification, beneficial ownership checks, risk scoring, and the collection and maintenance of KYC data. Screening tools test customers, counterparties, and transactions against sanctions, watchlists, politically exposed person data, and adverse media sources. Transaction monitoring systems assess payment and account activity against scenarios, rules, typologies, and risk indicators designed to identify unusual or suspicious behavior. Case management platforms then organize alerts, investigations, evidence, audit trails, escalation decisions, and reporting workflows. In more advanced environments, these capabilities are supported by network analytics, entity resolution, digital identity tools, and data-integration layers that help connect fragmented risk signals across systems. FATF’s guidance on digital identity and collaborative analytics is especially relevant to this broader model.
The value of AML software lies not simply in automation, but in consistency, coverage, and the ability to link data points that would otherwise remain isolated. For example, transaction monitoring software can compare actual customer activity against expected behavior and identify patterns associated with layering, pass-through activity, unusual counterparties, or sudden shifts in volume and velocity. Screening software can identify links to sanctions or higher-risk persons and entities. Case management tools can preserve the rationale behind investigative decisions and provide an audit trail for quality assurance, internal audit, and regulatory review. This matters because AML effectiveness depends not just on detecting suspicious activity, but on being able to evidence why alerts were generated, how they were reviewed, and what action was taken in response. The FCA’s guidance explicitly treats transaction monitoring as part of an integrated financial crime control process rather than a siloed system.
Watch on YouTube: Anti-Money Laundering (AML) Software
At the same time, AML software should not be mistaken for automatic compliance. One of the most common weaknesses in AML programmes is the assumption that buying a system is equivalent to solving the problem. In reality, software is only as effective as the data feeding it, the scenarios and thresholds configured within it, the governance overseeing it, and the investigators using it. Poor data quality, fragmented customer records, weak scenario calibration, excessive false positives, inadequate tuning, and weak ownership can all reduce software effectiveness significantly. Regulatory expectations remain focused on outcomes, not vendor claims. Firms must therefore be able to demonstrate that their software is appropriate for their specific business model, risk profile, and operational environment.
This is why the risk-based approach remains central to AML software design. A firm should not configure its systems in the same way for all products, customers, jurisdictions, or delivery channels. Higher-risk business lines may require more sensitive monitoring scenarios, more frequent screening refreshes, stronger onboarding controls, or more detailed case escalation rules. Lower-risk activity may justify simpler or more targeted controls. FATF’s long-standing guidance for the banking sector makes clear that institutions are expected to identify, assess, and understand their money laundering and terrorist financing risks and apply controls proportionately. AML software should therefore be aligned to the institution’s financial crime risk assessment, not treated as a generic plug-in applied uniformly across the organization.
Transaction monitoring is one of the most visible uses of AML software, but also one of the most misunderstood. A monitoring engine does not “detect money laundering” directly. It detects patterns, anomalies, and rule triggers that may indicate suspicious behavior and require review. These can include unusual transaction values, round-dollar transfers, rapid movement of funds, structuring behavior, activity inconsistent with customer profile, or network patterns suggestive of layering. The software’s role is to surface activity worthy of investigation, not to make the final legal or compliance judgment on its own. The FCA’s current guidance on transaction monitoring highlights implementation, oversight, and responsible innovation, which reinforces the point that monitoring software must be managed as a living control, not as a static one-time implementation.
Screening technology is another critical area. AML software often includes sanctions screening, politically exposed person screening, and adverse media functionality at onboarding and on an ongoing basis. These tools help institutions identify whether a customer, beneficial owner, connected party, or transaction counterparty presents elevated legal, regulatory, or reputational risk. However, screening effectiveness also depends heavily on data quality, name-matching logic, transliteration handling, false-positive management, and the ability to investigate and disposition matches consistently. Weak screening governance can create either over-alerting, which overwhelms teams, or under-detection, which creates obvious regulatory exposure. This is one reason AML software must be embedded within broader governance and quality assurance structures rather than treated as a purely technical implementation.
Increasingly, AML software is also expected to support a more connected financial crime framework. Fraud, cyber-enabled crime, mule activity, sanctions evasion, and money laundering are often operationally linked. FinCEN has highlighted that cyber-events and cyber-enabled crime intersect with BSA/AML obligations, and FATF has discussed data pooling and collaborative analytics as ways to improve detection of suspicious patterns that may not be visible inside a single narrow dataset. This means modern AML software is moving away from purely rules-based transaction review toward broader data integration, cross-channel intelligence, and in some cases machine learning or graph-based analysis. Even so, regulators have not abandoned the requirement for explainability, validation, and defensible control design. New technology may strengthen AML capability, but it must remain understandable, testable, and proportionate.
Governance is therefore one of the most important dimensions of AML software. Firms need clear ownership for system design, scenario development, threshold tuning, model validation, alert handling, issue remediation, and change management. They also need management information that allows senior leadership to understand whether the software is producing meaningful alerts, whether investigation backlogs are emerging, whether typologies are being captured effectively, and whether the system still reflects the institution’s current risks. A technically advanced platform with weak governance can fail just as badly as a simpler one. Regulatory guidance consistently points back to systems and controls, not just systems alone.
A further consideration is that AML software must support evidencing as much as detection. In regulatory terms, it is not enough for a firm to say that a system is in place. It must be able to show how alerts are generated, how changes were approved, how scenarios were calibrated, what testing was performed, how investigators reached conclusions, and how suspicious activity reporting decisions were made. This evidential layer is essential for internal audit, regulatory review, and remediation work. Case management, alert disposition tracking, and historical audit trails are therefore not secondary features; they are part of what makes AML software operationally credible.
Ultimately, AML software is a critical component of the financial crime control environment because it allows institutions to apply AML obligations at a scale and level of complexity that manual processes alone cannot support. It helps firms monitor customers, screen risk, investigate unusual activity, document decisions, and respond to emerging typologies across products and channels. But its real value depends on something deeper than automation: alignment to risk, strong data, effective governance, and professional investigative judgment. In a modern financial crime environment, the question is not whether a firm has AML software, but whether that software is configured, governed, and used in a way that produces a credible and defensible AML outcome.




