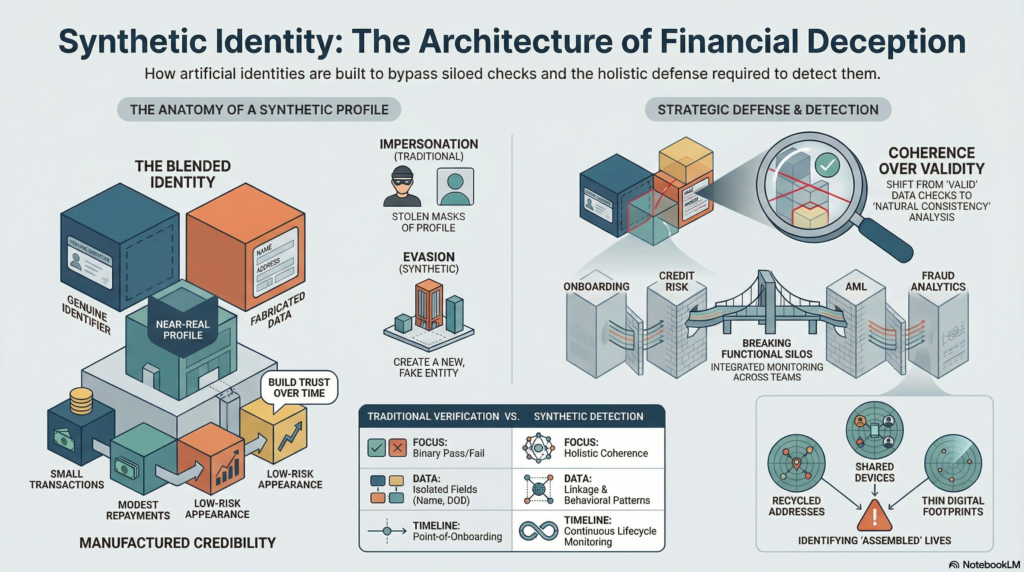
Synthetic identity is a complex financial crime typology in which a criminal creates a false identity by combining real and fabricated information to form a profile that appears legitimate enough to pass onboarding, obtain products, build transactional history, or evade suspicion. Unlike traditional identity theft, which involves impersonating a real person directly, synthetic identity abuse often relies on constructing a partially fictitious identity that does not belong wholly to any one individual. The resulting profile may contain a genuine national identifier, address, phone number, or date of birth combined with invented names, altered personal details, or manipulated supporting data. In the financial crime environment, this makes synthetic identity particularly dangerous because it does not always present as an obvious impersonation case. Instead, it creates an artificial customer that can look increasingly credible over time.
From a professional financial crime perspective, synthetic identity is not simply an onboarding fraud issue. It is a control evasion strategy that can affect customer due diligence, fraud detection, credit underwriting, account monitoring, and money laundering controls. The criminal objective is often to establish a relationship that appears low risk at first, nurture it gradually, and then exploit the resulting trust for financial gain. This may involve opening deposit accounts, obtaining payment products, building credit lines, receiving disbursements, or using the account as a vehicle for fraudulent or suspicious fund flows. The threat is significant because the institution may believe it has onboarded a legitimate customer when, in reality, it has created access for a criminally controlled profile that was designed specifically to survive basic verification checks.
Synthetic identity abuse is especially challenging because it exploits the structural logic of identity verification. Many financial institutions rely on matching identity elements across documents, databases, device signals, and customer-provided data. A synthetic identity is designed to satisfy enough of those checks to appear plausible, even where the overall profile is false in substance. A real identifier may validate successfully, an address may exist, an email may function, and a device may appear stable. If those elements are viewed in isolation, the customer can appear genuine. The weakness emerges when the institution fails to identify that the identity lacks natural consistency, credible history, or authentic linkage between its component parts. In this way, synthetic identity attacks not only individual controls, but the assumptions underlying the institution’s identity framework.
One of the defining characteristics of synthetic identity is that it often develops over time rather than being used immediately for a single fraudulent event. Criminals may create a synthetic profile, establish an account with limited functionality, interact with the institution in a low-risk manner, and then gradually deepen the relationship. This can include small transactions, regular account activity, modest repayment behaviour, or requests for additional services designed to build credibility. Once the profile has accumulated enough apparent legitimacy, it may be used to obtain larger credit exposures, conduct more significant transactions, or support other forms of fraud and laundering. This patient and staged approach makes synthetic identity different from many fast-moving fraud typologies. It is often designed to mature within the financial system before being exploited fully.
Watch on YouTube: Synthetic Identity
In the financial crime environment, the implications go beyond direct fraud losses. A synthetic identity can be used to open accounts that receive the proceeds of scams, support mule activity, facilitate layering, obscure beneficial ownership, or create transactional pathways that appear detached from known high-risk actors. Because the identity itself is not wholly real and not wholly fictitious, it can be difficult for institutions to classify and investigate using traditional fraud categories. It may not trigger obvious identity theft indicators because no single victim is being impersonated in a complete sense, and it may not trigger conventional KYC concerns if the component data appears valid. This is what makes synthetic identity such a serious threat for firms relying on fragmented or overly static identity controls.
The typology also has important links to credit risk and payment fraud. Synthetic profiles are frequently used to obtain credit products, cards, loans, overdrafts, or financing facilities that would not be extended to an obviously fabricated customer. In these cases, the criminal objective may be to build repayment history initially and then default after reaching a higher exposure threshold. In other scenarios, synthetic accounts are used more transactionally, serving as channels for receiving funds, conducting fraudulent purchases, or moving value through the financial system. This overlap means synthetic identity should not be managed solely by fraud or onboarding teams. It sits at the intersection of fraud risk, AML exposure, credit abuse, and wider financial crime governance.
A central challenge for institutions is that synthetic identity often appears credible when assessed through narrow control points. Documentary evidence may be present, device usage may seem normal, and the customer journey may not contain dramatic anomalies. The problem becomes visible only when the firm examines the identity holistically. Does the profile show natural consistency across age, contact information, digital footprint, address history, product usage, and behavioural patterns? Are there signs that the identity has been assembled rather than lived? Is the account linked to shared devices, repeated contact points, recycled addresses, unusual application patterns, or other profiles with overlapping elements? Mature synthetic identity detection depends on this broader contextual analysis rather than simple pass-fail verification at onboarding.
A professionally robust control framework therefore treats synthetic identity as a lifecycle risk. Prevention begins with strong onboarding design, but it cannot end there. Institutions need controls that assess the coherence of an identity, not just the validity of individual fields. This may include deeper cross-element verification, device and behavioural analysis, velocity monitoring across applications, scrutiny of digital and contact-linkage patterns, and challenge where identity elements appear technically valid but contextually weak. Institutions should also be cautious where identity evidence is unusually thin, recently created, or inconsistent with the product being requested. The most effective frameworks distinguish between a customer who can provide valid information and a customer whose identity makes natural sense across the wider relationship.
Detection during the life of the account is equally important. Synthetic identities often reveal themselves through patterns that emerge only after onboarding. These may include unusual transaction behaviour, linked-party relationships, repeated use of shared identifiers, sudden shifts in product usage, irregular repayment conduct, concentration of activity around similar customer clusters, or account use that suggests external orchestration rather than ordinary personal or business behaviour. Where synthetic identity is being used for laundering or mule purposes, the account may also show suspicious payment flows, rapid dispersal of funds, or connections to known fraud typologies. This is why firms need close coordination between onboarding, fraud analytics, transaction monitoring, credit risk, and investigations functions. A synthetic identity may pass one team’s controls while generating subtle concerns elsewhere.
Operational response also matters. Once suspected, a synthetic identity case requires more than simple account restriction. The institution may need to investigate whether the profile is linked to other accounts, applications, devices, or beneficiaries; whether the activity indicates organized criminal behaviour; whether products were obtained under false pretences; and whether suspicious activity reporting or wider remediation is required. The review should also examine whether the case reflects a one-off failure or a broader control weakness affecting customer acquisition, credit approval, identity verification, or network detection. Synthetic identity investigations are therefore often as much about systemic learning as individual case resolution.
Governance is a critical part of managing this risk. Synthetic identity should feature explicitly in financial crime risk assessments, fraud typology inventories, onboarding governance, model validation, and control testing. Institutions should understand which products, channels, geographies, and customer segments are most vulnerable, and whether current controls are capable of identifying identities that are plausible in form but false in substance. Useful metrics may include linked-identity clusters, repeat application overlaps, false-positive outcomes in identity screening, delayed-confirmation fraud cases, early-life account anomalies, and credit-loss patterns associated with weak identity coherence. Without this level of oversight, synthetic identity can remain hidden within broader fraud or credit-loss categories and fail to receive the strategic attention it warrants.
There is also an important organizational mindset issue. Many firms are well prepared to detect stolen identities or overt impersonation, but less prepared to identify entirely manufactured customer profiles. Synthetic identity requires institutions to move beyond binary thinking about whether an identity is “real” or “fake.” In practice, the more relevant question is whether the identity is authentic, attributable to a real and rightful individual, and behaving in a manner consistent with that claimed existence. That is a more demanding standard, but it is essential in a financial crime environment where criminals increasingly exploit the gaps between compliance checks, fraud systems, and operational silos.
Ultimately, synthetic identity is a serious financial crime threat because it manufactures credibility inside the financial system. It enables criminals to create customer relationships that appear legitimate, survive basic verification, and later serve as vehicles for fraud, credit abuse, mule activity, and illicit fund movement. In modern financial services, the challenge is no longer limited to confirming that data points exist or that documents can be matched. It is determining whether the identity presented is coherent, authentic, and genuinely controlled by the person it claims to represent. For that reason, synthetic identity should be treated as a core financial crime risk requiring integrated controls, continuous monitoring, strong investigative capability, and close coordination across fraud, AML, onboarding, credit, and governance functions.