Account takeover, commonly abbreviated as ATO, is a financial crime typology in which a criminal gains unauthorized control of a legitimate customer account and then uses that access to steal funds, obtain data, alter account settings, or facilitate wider criminal activity. In the financial crime environment, ATO is not just a digital-security problem. It is a control-integrity issue that can affect fraud prevention, anti-money laundering, customer due diligence, payment security, and operational resilience at the same time. Official financial-sector guidance treats compromised credentials and unauthorized access as material risks requiring layered controls rather than a single-point authentication response.
What makes ATO especially serious is that the criminal is operating through an account that already appears legitimate. The relationship has usually passed onboarding, identity verification, and normal account setup, and may also have established transaction history, known devices, and familiar servicing patterns. Once that trusted environment is compromised, the offender can exploit the institution’s confidence in the existing relationship. This gives ATO a different risk profile from many other fraud types. The criminal does not necessarily need to create a false customer; instead, they weaponise a real one. In practice, this can allow suspicious activity to blend into ordinary customer behavior long enough to execute payments, change contact details, add beneficiaries, or suppress alerts.
ATO usually begins with the compromise of credentials, identity information, or trusted access mechanisms. That compromise may arise through phishing, social engineering, malware, data breaches, credential reuse, or manipulation of account-recovery processes. Financial regulators and sector guidance increasingly stress that institutions must assume valid credentials can still be misused and should therefore design multiple layers of control to address the risk posed by compromised credentials. That principle is central to understanding ATO in a financial crime context: the question is not simply whether the right password or login factor was used, but whether the person exercising control is genuinely the rightful customer.
The consequences of ATO extend well beyond unauthorized login. Once access is established, the account can be used to initiate transfers, access stored payment methods, change passwords, register new devices, request replacement cards, alter security settings, or review customer data for future fraud. In some cases the compromise is exploited immediately for rapid value extraction. In others, the offender first studies the account, tests what controls can be bypassed, and only later initiates transactions. This staged behavior is one reason ATO can be hard to detect: the first visible sign of compromise may not be a payment at all, but a quiet sequence of profile amendments and authentication changes that weaken the customer’s ability to recover control.
Watch on YouTube: Account Takeover (ATO)
From a financial crime perspective, ATO matters because it can function as both a fraud event and a gateway to wider illicit activity. A compromised account may be used to transfer funds to mule accounts, support unauthorized card usage, facilitate social-engineering scams, or move proceeds onward through accounts that appear genuine. This creates direct overlap between fraud risk and laundering risk. If a legitimate customer account is used as a temporary conduit for suspicious transfers, the institution is not dealing only with customer compromise; it is also confronting the possibility that criminal proceeds are being layered through apparently clean account infrastructure. That is why ATO should be assessed not merely as an account-security incident, but as a potentially broader financial crime case.
The typology is particularly important in digital financial services environments. Mobile banking, real-time payments, self-service profile changes, and remote servicing all increase convenience for genuine customers, but they also reduce the time available to detect and stop criminal misuse once a compromise occurs. Faster payment environments can compress the intervention window to minutes. Where an attacker takes over an account and immediately creates a new payee or redirects funds, the institution may have very little opportunity to prevent loss unless monitoring is both dynamic and near real time. Financial-sector assessment frameworks explicitly point to the need to correlate anomalous login and fraud signals across business units to detect multifaceted attacks.
A mature approach to ATO therefore depends on layered prevention rather than reliance on any single safeguard. Strong authentication remains essential, but it is not enough on its own. Institutions need controls around credential recovery, device enrollment, account changes, new payee setup, and high-risk transactions. They also need to think in terms of attack chains rather than isolated events. A login from an unfamiliar device may be explainable on its own. A login from an unfamiliar device followed by a password reset, mobile-number change, and immediate outbound payment to a new beneficiary is a very different scenario. Effective ATO defence depends on linking those events together quickly enough to alter the risk decision before funds leave the institution.
Detection capability is therefore as important as authentication. ATO controls should monitor for anomalies in login behavior, geolocation, device usage, session patterns, failed access attempts, changes to customer profile data, abnormal servicing requests, and payment behavior inconsistent with the customer’s normal history. Institutions that treat fraud monitoring, security logging, and account-servicing oversight as separate disciplines often miss the full pattern. By contrast, firms that correlate access anomalies with downstream customer actions are better placed to identify when valid credentials are being used in an invalid context. Sector guidance on authentication and cybersecurity assessment supports this risk-based, multi-signal approach.
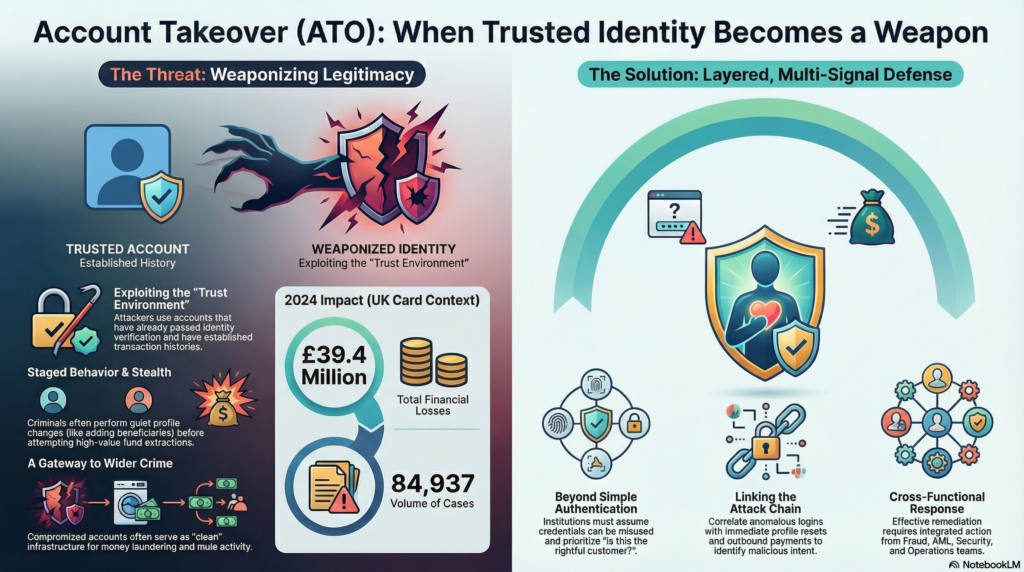
Operational response is also critical once ATO is suspected. Restricting access, suspending suspicious payments, reversing recent profile changes, re-establishing trusted contact with the customer, and reviewing linked transactions are all part of an effective response. In more serious cases, the institution may also need to assess whether the compromised account has been used to receive or move proceeds connected to wider fraud or mule activity. This makes ATO investigation inherently cross-functional. Fraud teams may focus on immediate loss prevention, while AML or financial crime teams assess suspicious flows, operations teams handle remediation, and security teams analyze compromise vectors. A fragmented response can leave important risks unaddressed even if the initial unauthorized payment is stopped.
Governance is another essential component. ATO should be reflected explicitly in fraud risk assessments, digital-channel control frameworks, authentication strategy, financial crime typologies, and management reporting. Firms need to understand which products, channels, and customer journeys are most exposed, whether existing controls are too dependent on static credentials, and whether incident data is being used to recalibrate controls effectively. Industry reporting illustrates that ATO remains material at scale: UK Finance’s 2025 Annual Fraud Report recorded £39.4 million in account takeover losses and 84,937 cases in 2024 in the UK card context alone. That level of volume shows that ATO is not an edge-case threat; it is an established and recurring component of the wider fraud landscape.
There is also a significant customer-harm dimension. ATO can deprive customers of funds, expose personal information, disrupt access to essential services, and undermine trust in digital channels. For firms, poor handling can create reputational damage and regulatory concern even where direct losses are limited. A professionally mature response therefore combines strong preventative controls with effective remediation, clear customer communication, and timely restoration of secure access. In financial crime terms, customer treatment is not separate from control quality; it is part of the institution’s ability to contain damage and preserve the integrity of the account relationship after compromise.
Ultimately, account takeover is a major financial crime threat because it converts legitimate customer infrastructure into a criminal asset. It allows offenders to act behind a trusted identity, bypass elements of the control framework, and move quickly from access compromise to fraud, data abuse, or suspicious fund movement. In modern financial services, it is no longer sufficient to verify customer identity once and then assume that valid access credentials prove ongoing legitimacy. Institutions need to assess continuously whether control of the account still rests with the rightful customer and whether the surrounding behavior supports that conclusion. For that reason, ATO should be treated as a core financial crime risk requiring integrated controls across authentication, fraud analytics, payment monitoring, investigations, operations, and governance.




