Identity theft is a significant financial crime typology in which a criminal unlawfully obtains and misuses another person’s personal, financial, or identifying information in order to impersonate them, access services, open accounts, move funds, evade controls, or facilitate wider criminal activity. In a financial crime context, identity theft is not simply a consumer fraud issue. It is a foundational enabler that can sit upstream of payment fraud, account takeover, mule activity, synthetic identity abuse, credit fraud, and money laundering exposure. Its importance lies in the fact that it attacks one of the core assumptions on which the financial system depends: that the identity presented to a firm is authentic, controlled by the rightful person, and reliable enough to support risk-based decision-making.
From a professional risk perspective, identity theft is best understood as a compromise of identity integrity across the customer lifecycle. It may begin with the theft of credentials, government-issued identifiers, banking details, contact information, device data, or documentary evidence, but its real significance emerges in how that information is used. Criminals can exploit stolen identity elements to open new accounts, apply for credit, bypass onboarding controls, reset access credentials, change account details, or support fraudulent transactions through accounts that appear legitimate on their face. Once identity integrity has been compromised, multiple downstream controls can be weakened because the institution may continue to rely on data that appears valid but is no longer under the control of the genuine individual.
The mechanics of identity theft are varied and often cumulative. Criminals may collect information through phishing, social engineering, malware, data breaches, document theft, compromise of digital channels, or exploitation of weak account recovery processes. In many cases, identity theft is not the result of a single sophisticated intrusion but of fragmented information gathered over time and assembled into a usable identity profile. A name, date of birth, email address, phone number, partial banking data, and leaked password may each appear low value in isolation, but together they can provide enough material to impersonate a customer, answer security questions, intercept communications, or pass superficial verification controls. That cumulative nature is what makes identity theft especially dangerous in modern financial services environments that rely heavily on remote interactions and digital onboarding.
Within the financial crime environment, identity theft has both direct and indirect consequences. Directly, it can result in unauthorized transactions, account openings, fraudulent lending, card misuse, and losses to customers or institutions. Indirectly, it can create a platform for more complex criminal conduct. A stolen identity can be used to establish accounts that receive the proceeds of fraud, disguise beneficial ownership, support layering activity, or provide legitimacy to transactions that would otherwise attract scrutiny. In that sense, identity theft should not be viewed purely as an endpoint offence. It often functions as an entry point into a larger ecosystem of financial crime in which fraud, impersonation, data misuse, and illicit fund flows reinforce one another.
Watch on YouTube: Identity Theft
One of the most important distinctions in this area is the difference between identity theft and related typologies such as identity fraud, synthetic identity abuse, and account takeover. Identity theft concerns the unlawful acquisition and misuse of real personal information. Identity fraud is the broader act of using that information deceptively. Synthetic identity abuse involves combining genuine and fabricated elements to construct a new profile that appears legitimate enough to obtain products or build transactional history. Account takeover, by contrast, involves gaining control of an existing legitimate account rather than creating a new relationship. In practice, these categories overlap extensively. A single criminal scheme may begin with identity theft, evolve into account compromise, and later result in new-account fraud or laundering activity. For financial crime teams, the operational lesson is that these risks should be managed as connected typologies rather than in isolation.
The impact on customer due diligence and onboarding controls is particularly serious. Financial institutions devote considerable effort to identifying and verifying customers at the point of entry, yet identity theft is specifically designed to exploit those controls. Where stolen documents, compromised personal data, or manipulated digital footprints are used successfully during onboarding, the firm may establish a relationship on a false premise while believing it has satisfied KYC requirements. Even if the identity belongs to a real person, the operative risk is that the person presenting it is not the rightful individual. This creates a critical weakness: the institution may onboard a relationship that appears compliant but is, in substance, under criminal control. That problem becomes more acute where firms over-rely on documentary checks, static credentials, or uncorroborated digital data without sufficient behavioural or contextual validation.
Identity theft also places pressure on ongoing monitoring frameworks. Once an account or product has been obtained using stolen identity information, later activity may appear ordinary unless the institution is capable of detecting inconsistencies between the known customer profile and actual account behaviour. This is why effective financial crime programmes treat identity assurance as a continuing obligation rather than a one-time onboarding exercise. The relevant question is not only whether the customer’s identity was verified when the relationship began, but whether the account continues to be operated by the rightful individual and whether subsequent changes in behaviour, contact details, transaction patterns, or channel usage suggest identity misuse. Without that dynamic perspective, firms can remain exposed long after the original compromise.
A mature control environment therefore addresses identity theft through layered prevention, detection, and response. Preventive controls typically include robust identity verification, stronger document validation, secure authentication, careful account recovery design, protection of customer-contact changes, and appropriate challenge for high-risk actions. Detection controls should focus on anomalies that may indicate identity misuse, such as inconsistencies in application data, unusual combinations of identity attributes, multiple relationships linked to overlapping identifiers, abrupt profile amendments, changes in device or channel patterns, and transactional behaviour inconsistent with the supposed customer profile. The most effective approaches do not rely on one control in isolation. They combine identity evidence, device intelligence, behavioural data, transactional context, and case management to build a more complete risk picture.
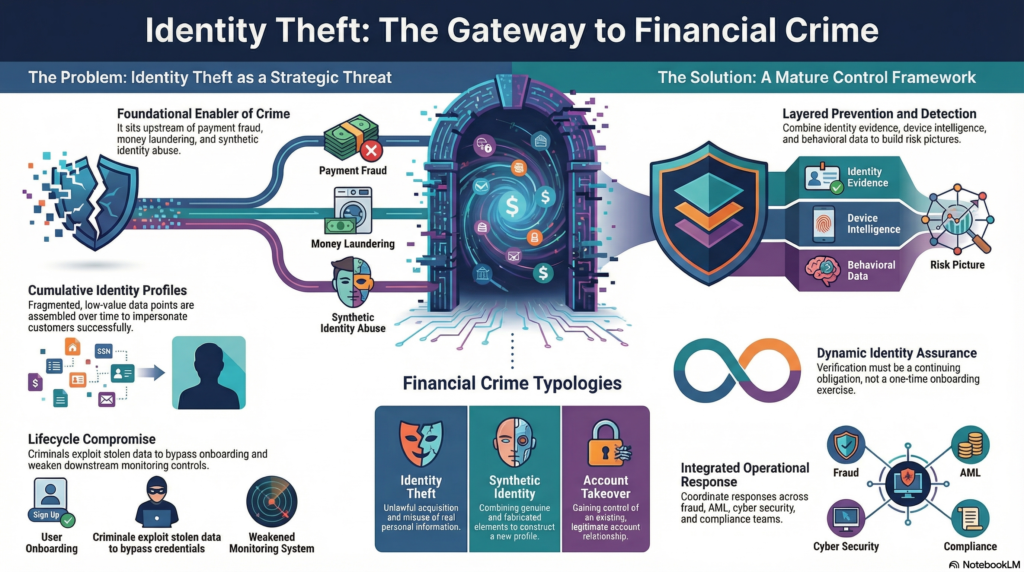
Operational response is equally important once identity theft is suspected. Firms need clear procedures to restrict misuse, investigate affected accounts, validate customer identity through trusted channels, remediate unauthorized activity, and consider whether the event has implications for wider fraud or AML exposure. In some cases, identity theft may appear initially as a customer complaint or service issue, but deeper review may reveal coordinated misuse across multiple accounts, shared devices, linked beneficiaries, or common data points indicating organized criminal activity. That is why identity theft cases often require coordinated handling across fraud operations, AML teams, cyber security, customer servicing, investigations, and compliance oversight. Treating the incident as a narrow authentication issue can cause firms to miss broader network risk.
Governance and risk assessment are also essential. Identity theft should feature explicitly in financial crime risk assessments, fraud typology libraries, onboarding risk frameworks, and control testing programmes. Institutions should understand which products, channels, geographies, and customer segments are most exposed, and whether control design reflects actual threat patterns rather than legacy assumptions. Metrics such as confirmed impersonation cases, new-account fraud linked to stolen identities, repeat use of shared identifiers, false-positive rates in identity screening, recovery times, and links to downstream mule activity can all help assess whether the framework is proportionate and effective. In professional terms, identity theft should be managed as a strategic control risk, not merely a sequence of individual incidents.
There is also a significant customer harm dimension. Identity theft can cause financial loss, denial of legitimate services, disruption to credit standing, loss of trust, and prolonged remediation burdens for victims. For financial institutions, poor handling of such cases can create regulatory, legal, and reputational exposure in addition to direct losses. A professionally mature response therefore requires both strong crime controls and thoughtful customer treatment. The institution must be able to act quickly to contain misuse while also restoring the legitimate customer’s position, re-establishing secure account control, and preserving confidence in the integrity of the relationship.
Ultimately, identity theft is a core financial crime risk because it allows criminals to manufacture legitimacy from stolen personal information. It can compromise onboarding, weaken authentication, distort transaction monitoring, and provide a gateway to fraud, account abuse, and illicit fund movement. In modern financial services, especially those built around remote onboarding and digital servicing, the challenge is no longer just verifying that an identity exists. It is determining whether the person presenting that identity is the rightful individual, whether control remains with them over time, and whether the surrounding behaviour supports that conclusion. For that reason, identity theft should be treated as a central component of the financial crime threat landscape, requiring integrated controls, strong governance, continuous reassessment, and close coordination across fraud, AML, cyber, and operational functions.




