Credential stuffing is a cyber-enabled financial crime technique in which criminals use large volumes of previously compromised usernames, email addresses, and passwords to attempt automated access to customer accounts across digital platforms. It relies on a simple but highly effective premise: many individuals reuse the same credentials across multiple services, allowing data exposed in one breach or compromise event to be exploited elsewhere. In the financial crime environment, credential stuffing is significant not merely because it can generate unauthorized access, but because it creates an entry point into a wider chain of fraud, account takeover, payment abuse, identity misuse, and illicit fund movement. It is therefore best understood not as a narrow login-security issue, but as a scalable method for converting stolen data into financial crime opportunity.
From a professional risk perspective, credential stuffing is dangerous because it industrializes account compromise. Unlike targeted attacks that focus on a single victim, credential stuffing is designed for volume. Criminals can test thousands or millions of credential pairs against online banking portals, payment services, e-commerce platforms, digital wallets, or other financial interfaces using automated tools, bot infrastructure, and anonymized networks. Even where the success rate is low, the economics remain attractive because a small number of successful logins can provide access to valuable accounts, stored payment methods, personal data, loyalty balances, or verified customer relationships. This scale makes credential stuffing especially relevant in modern financial services environments where digital access is central to customer interaction and product delivery.
The technique is rooted in credential compromise, but its real significance lies in what happens after access is gained. A successful credential stuffing attack may allow a criminal to take over a legitimate account, review account balances, change contact details, reset authentication settings, add payees, initiate transactions, or harvest further personal and financial information for later use. In some cases, the account is monetized directly through unauthorized transfers or card usage. In others, the compromise serves as a staging point for broader criminal activity, such as mule account operation, application fraud, social engineering, or laundering of proceeds. This makes credential stuffing an upstream enabler within the financial crime lifecycle rather than a self-contained event.
One of the reasons credential stuffing is so effective is that it exploits trust in valid credentials. From the system’s perspective, a correct username and password may look like legitimate customer access, especially where additional authentication layers are weak, inconsistently applied, or vulnerable to circumvention. This creates a serious control challenge. Many institutions still treat authentication as a point-in-time gate rather than a dynamic risk process. Credential stuffing exposes the weakness in that approach. The issue is not only whether credentials are valid, but whether the context of their use is consistent with genuine customer behaviour. If that contextual analysis is absent, a criminal can operate under the appearance of legitimacy using nothing more than reused credentials acquired elsewhere.
Watch on YouTube: Credential Stuffing
In the financial crime environment, the impact of credential stuffing extends beyond the initial account compromise. Once access is obtained, downstream controls may be weakened because the session appears tied to a genuine customer identity and an established relationship. Transactions may initially appear less suspicious, especially where the criminal moves cautiously, studies account behaviour before acting, or manipulates the account in stages. A common pattern is for the offender to log in, survey the account, test whether security settings can be changed, and only later initiate payments or profile amendments. In some cases, criminals use the access to collect intelligence for future fraud rather than to steal immediately. This delayed exploitation can make detection more difficult and increase the risk that the compromise will be underestimated.
Credential stuffing also illustrates the convergence of cyber, fraud, and financial crime risk. The initial compromise is often enabled by data breaches, malware, phishing, or illicit credential markets, all of which sit within the cyber-enabled crime ecosystem. The subsequent abuse may involve account takeover, payment fraud, loyalty fraud, identity theft, or money laundering through compromised or linked accounts. As a result, institutions should avoid treating credential stuffing purely as an information security problem. It has direct implications for fraud losses, customer harm, AML exposure, operational resilience, and regulatory accountability. A control framework that separates these issues too rigidly will often detect them too late or respond to them in fragmented ways.
The typology is particularly challenging because successful attacks do not always require sophisticated compromise of the institution’s systems. The institution’s infrastructure may be functioning exactly as designed, yet still be abused because the customer’s credentials have been compromised elsewhere and reused. This shifts part of the risk from internal system breach to external ecosystem exposure. Financial institutions must therefore defend not only against attacks on their own platforms, but also against the downstream consequences of breaches, phishing campaigns, and credential theft occurring beyond their immediate perimeter. In professional terms, credential stuffing is a third-party and ecosystem risk as much as it is a platform-security issue.
A mature financial crime response to credential stuffing begins with recognition that authentication alone is not sufficient. Preventive controls should include strong password hygiene requirements, resistance to automated login abuse, rate limiting, bot detection, device intelligence, challenge mechanisms, and robust multi-factor authentication. However, even these measures are not complete solutions. Attackers adapt quickly, distribute attempts across infrastructure, mimic human behaviour, and target weaker recovery or step-up journeys where front-door controls are stronger. For that reason, institutions need layered defence that treats login attempts, account behaviour, and transaction activity as connected components of the same risk picture.
Detection capability is central to effective control. Institutions should monitor for patterns consistent with credential stuffing, such as elevated failed-login volumes, distributed access attempts across multiple accounts, unusual login velocity, repeated attempts from rotating infrastructure, anomalous device behaviour, or clusters of accounts experiencing similar access patterns. But technical detection of attack traffic is only one part of the problem. Firms also need to identify the behavioural consequences of successful compromise. These may include sudden credential resets, new device enrollment, changes to contact information, unusual navigation behaviour, creation of new beneficiaries, access at atypical times, or transactions inconsistent with the customer’s normal profile. The strongest frameworks connect these upstream and downstream indicators so that successful logins are not assessed in isolation from later suspicious activity.
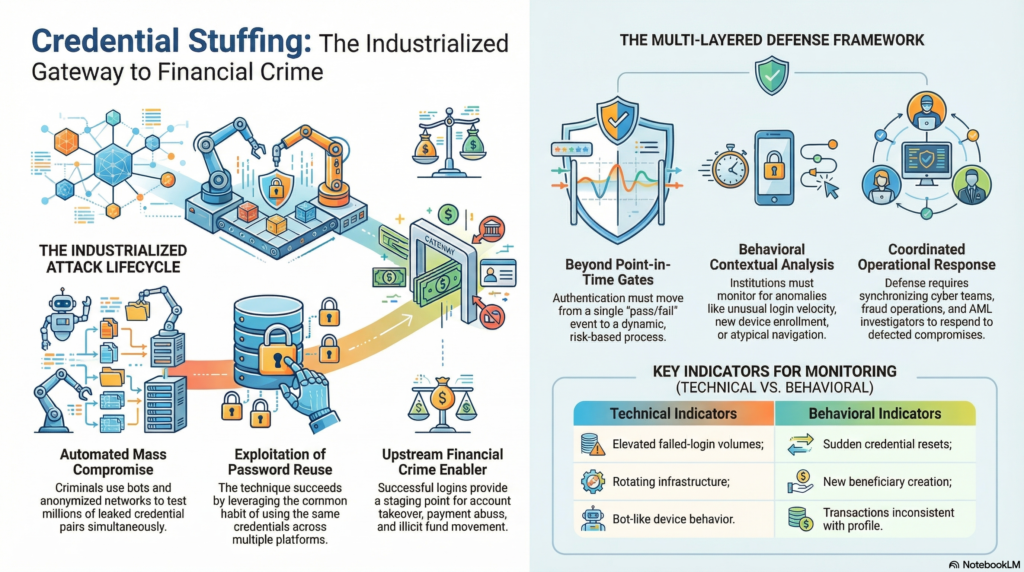
Operational response must also be disciplined and coordinated. Once credential stuffing is detected or strongly suspected, the institution may need to block attack traffic, lock or challenge affected accounts, force credential resets, review recent changes, assess linked payment activity, and determine whether any compromised accounts have already been used for fraud or suspicious fund flows. Where unauthorized access has occurred, the review should extend beyond the login event itself. Investigators should consider whether customer data was harvested, whether other products or services tied to the account were exposed, whether the compromise affected identity assurance, and whether there are indicators of broader organized abuse across the customer base. This often requires coordination between cyber teams, fraud operations, AML investigations, customer service, and risk governance.
Governance is an essential part of managing credential stuffing as a financial crime risk. The typology should be reflected in fraud risk assessments, cyber-fraud control frameworks, digital channel governance, authentication strategy, and management information. Institutions need to understand which products, platforms, channels, and customer segments are most exposed, and whether existing controls are calibrated to automated and distributed attack patterns rather than only traditional account compromise scenarios. Useful metrics may include attack volumes, success rates, percentage of accounts requiring intervention, downstream fraud losses, customer-impact measures, false-positive rates, and recurrence by channel or product. Without this level of oversight, credential stuffing can be misclassified as routine login noise rather than recognized as a material financial crime threat.
There is also a significant customer and reputational dimension. Because credential stuffing often exploits password reuse and data compromise outside the institution’s direct control, customers may not understand how the compromise occurred or may perceive it as a failure of the institution regardless of the root cause. Poor communication, delayed response, or inadequate remediation can therefore damage trust even where direct financial losses are limited. Institutions need response processes that protect customers, re-establish secure access, and communicate clearly about the risk without shifting responsibility in a way that appears dismissive or operationally weak.
Ultimately, credential stuffing is a serious financial crime enabler because it transforms compromised credentials into scalable unauthorized access to legitimate accounts. It exploits weaknesses in authentication, customer behaviour, and digital ecosystem trust to create opportunities for account takeover, payment fraud, data theft, and wider criminal exploitation. In an environment where digital access is central to financial services and credential compromise is persistent across the broader online economy, this typology cannot be managed as a technical nuisance alone. It requires an integrated financial crime approach combining cyber defence, fraud detection, behavioural monitoring, account-protection controls, investigative capability, and strong governance. Only by treating credential stuffing as part of the wider financial crime landscape can institutions build a response that is proportionate, resilient, and operationally credible.