Card-not-present fraud is a major payment fraud typology in which a criminal uses stolen, compromised, or fraudulently obtained card details to conduct transactions where the physical card is not presented to the merchant. It is most commonly associated with e-commerce, mobile commerce, telephone orders, subscription services, digital wallets, and other remote payment environments. In the financial crime context, card-not-present fraud is significant not only because of the direct financial losses it causes, but because it reflects broader weaknesses in identity assurance, payment authentication, merchant controls, and transaction monitoring. It is a fraud type that sits at the intersection of payment risk, cyber-enabled crime, account compromise, identity theft, and wider financial crime activity.
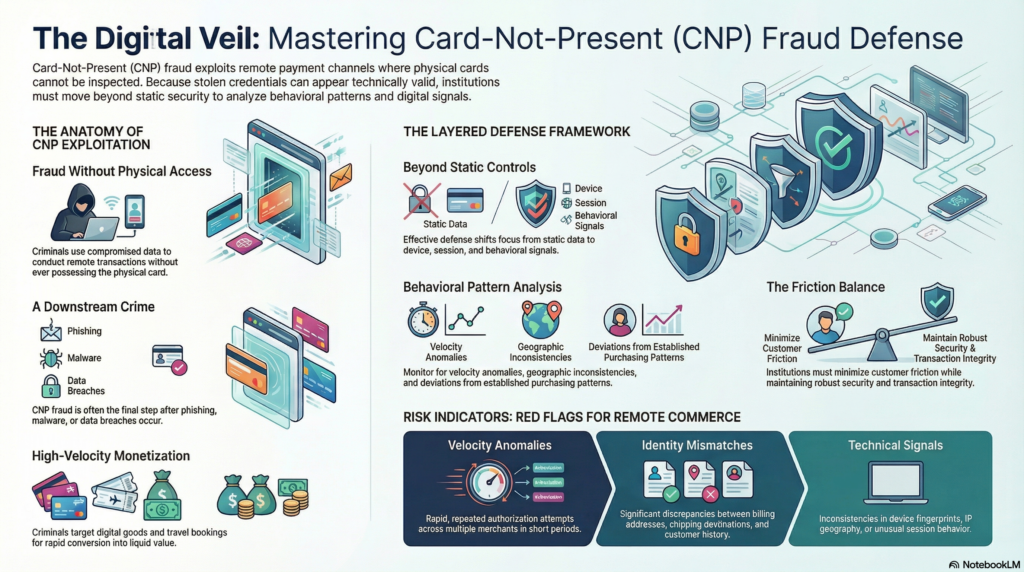
What makes card-not-present fraud particularly challenging is that the transaction can appear technically valid even when it is criminal in substance. The card number, expiry date, billing details, and security code may all be correct, yet the person using them is not the legitimate cardholder. In remote commerce environments, the merchant cannot rely on physical card inspection, chip authentication, or face-to-face verification. This means that the transaction must be assessed through alternative indicators such as device data, behavioural signals, customer history, billing and shipping consistency, merchant context, authentication outcomes, and broader transaction patterns. The fraud risk does not arise simply because the card is absent, but because the absence of physical verification shifts the entire burden of trust onto digital and behavioural controls.
In practice, card-not-present fraud is usually enabled by the compromise of payment credentials or related identity data. Criminals may obtain card details through phishing, malware, data breaches, account takeover, merchant compromise, skimming of stored credentials, social engineering, or the purchase of stolen card data from illicit networks. In many cases, the card details are only one component of the attack. Supporting information such as the cardholder’s name, billing address, phone number, email address, or one-time authentication data may also be acquired or manipulated to increase the likelihood of successful authorization. This means card-not-present fraud should not be viewed as a standalone card issue. It often represents the downstream use of credentials and personal data that have already been compromised elsewhere.
From a financial crime perspective, the typology is important because it demonstrates how criminal value can be extracted without direct access to the physical payment instrument. The payment card becomes a remote channel through which criminals can monetize stolen data rapidly and at scale. Fraudsters often test cards using small-value transactions before escalating to higher-value purchases, repeated attempts across multiple merchants, or automated attacks designed to identify valid credentials. Once successful, the criminal may obtain goods, digital services, gift cards, cash-equivalent value, or resaleable products. In some cases, compromised cards are also used to fund further criminal activity, including the purchase of services that support fraud operations or the movement of value into more opaque channels.
Watch on YouTube: Card-Not-Present Fraud
Card-not-present fraud is especially prevalent in digital commerce because of the speed, scale, and fragmentation of the ecosystem. Transactions may be initiated across multiple devices, geographies, merchants, and payment interfaces in very short periods of time. Merchants often prioritize seamless checkout, fast conversion, and low customer friction, which can inadvertently create conditions that criminals exploit. The same commercial pressures that drive simple payment experiences for genuine customers can reduce the number of barriers facing a fraudster using stolen card data. As a result, the control environment must balance customer convenience with transaction integrity, and institutions that get this balance wrong may either suffer elevated fraud losses or impose excessive friction on legitimate commerce.
A core challenge in managing card-not-present fraud is distinguishing between legitimate remote commerce and deceptive use of valid-looking payment credentials. Unlike counterfeit card fraud, where the fraud may be linked to a physical instrument, or card-present fraud, where point-of-sale controls play a larger role, card-not-present fraud is highly dependent on context. A transaction may look normal in value and merchant type, but still be suspicious when viewed alongside surrounding signals such as a new device, unusual velocity, multiple failed attempts, mismatched delivery details, recent account changes, or deviations from the customer’s established purchasing behaviour. This is why static controls are rarely sufficient on their own. Effective defence depends on combining payment data with identity, device, session, and behavioural intelligence.
In the broader financial crime environment, card-not-present fraud also has implications for merchant risk and acquiring oversight. Not all exposure sits with the issuing side. Merchants and payment service providers can be exploited through weak checkout controls, inadequate velocity monitoring, poor customer verification, and ineffective fraud screening. Certain merchant categories are more vulnerable because the goods are easily transferable, quickly delivered, digitally fulfilled, or readily monetised. Digital goods, gift cards, travel bookings, subscription services, and high-demand consumer products are all common targets because they can be acquired quickly and converted into value before the fraud is detected. This means card-not-present fraud should be considered not only as a customer payment issue, but as a commercial ecosystem risk involving merchants, acquirers, gateways, and service providers.
The relationship between card-not-present fraud and wider financial crime is also important. While the immediate event is usually categorized as payment fraud, the underlying activity may be linked to organized criminal networks, money mule arrangements, identity theft, or account compromise. Goods obtained through fraudulent card use may be resold, used in further criminal operations, or converted into more liquid forms of value. Fraud proceeds may move through merchant accounts, logistics channels, secondary marketplaces, or linked bank accounts. This is why institutions should avoid treating card-not-present fraud purely as a chargeback or dispute issue. In many cases, it is part of a broader criminal flow that includes compromised credentials, mule usage, collusive activity, and the laundering of proceeds.
A mature control framework for card-not-present fraud requires layered prevention, detection, and response. Preventive controls often include strong customer authentication, tokenization, card security measures, device fingerprinting, merchant verification tools, address and identity consistency checks, and risk-based friction at checkout. However, preventive controls alone are not enough. Fraudsters adapt quickly, and some will successfully bypass or defeat front-end controls. Detection capability must therefore identify suspicious transaction patterns in real time or near real time. Relevant signals include velocity anomalies, repeated authorization attempts, unusual merchant concentrations, mismatched billing and shipping data, geographic inconsistencies, unusual spend categories, and deviations from established customer behaviour. The strongest models assess the transaction as part of a broader behavioural pattern rather than as an isolated payment instruction.
Operational response is equally important. Once suspicious card-not-present activity is detected, institutions may need to decline or challenge transactions, block compromised cards, contact customers, investigate linked spending, review digital wallet usage, and assess whether the event suggests account takeover or wider identity compromise. Where the fraud pattern appears organized or repeated across multiple customers or merchants, the matter may require broader investigation across fraud operations, merchant risk teams, AML teams, and cyber functions. Weak coordination between these areas can lead to fragmented responses, where immediate losses are addressed but the wider criminal pattern is not recognized.
Governance and assurance also matter. Card-not-present fraud should feature in fraud risk assessments, payment product reviews, merchant monitoring frameworks, transaction screening design, and management reporting. Institutions need to understand which card portfolios, merchant categories, geographies, digital channels, and authentication paths generate the highest exposure. They also need meaningful metrics, such as authorization fraud rates, false-positive volumes, merchant concentration risk, chargeback trends, detection speed, loss severity, and repeat compromise indicators. Without this level of oversight, institutions may underestimate the extent to which card-not-present fraud reflects structural weaknesses in remote payment control environments.
There is also a customer and reputational dimension. Card-not-present fraud can undermine confidence in digital commerce, create frustration through declined legitimate transactions, and expose customers to financial loss or account disruption. For institutions, the challenge is to protect transactions without eroding trust through excessive friction or poor remediation. A professionally mature response therefore requires both strong controls and effective customer treatment. Genuine customers need confidence that remote transactions are secure, that suspicious activity will be detected promptly, and that the institution can respond quickly and fairly when fraud occurs.
Ultimately, card-not-present fraud is a core financial crime threat because it allows criminals to exploit remote payment channels without possessing the physical card. It turns stolen payment data into immediate transactional capability and exposes weaknesses across authentication, merchant controls, behavioural monitoring, and ecosystem coordination. In a modern commerce environment defined by digital transactions, fast checkout, and globally distributed payment infrastructure, this typology cannot be addressed through static card security measures alone. It requires an integrated financial crime approach combining payment fraud controls, identity assurance, merchant risk management, behavioural analytics, operational investigation, and strong governance. Only by treating card-not-present fraud as part of the wider financial crime landscape can institutions build defences that are proportionate, resilient, and effective.