Application fraud is a financial crime typology in which a person seeks to obtain a product, service, account, facility, or commercial relationship by providing false, misleading, manipulated, or incomplete information during the application process. In the financial crime environment, this can include the use of stolen identities, synthetic identities, falsified documents, concealed ownership structures, misrepresented income, fabricated business activity, or deceptive explanations regarding the intended use of an account or product. Although often viewed as an onboarding issue, application fraud is more than a front-end fraud event. It is a method of entering the financial system under false pretences, and once successful, it can create exposure across fraud, anti-money laundering, sanctions, credit risk, and wider control failure.
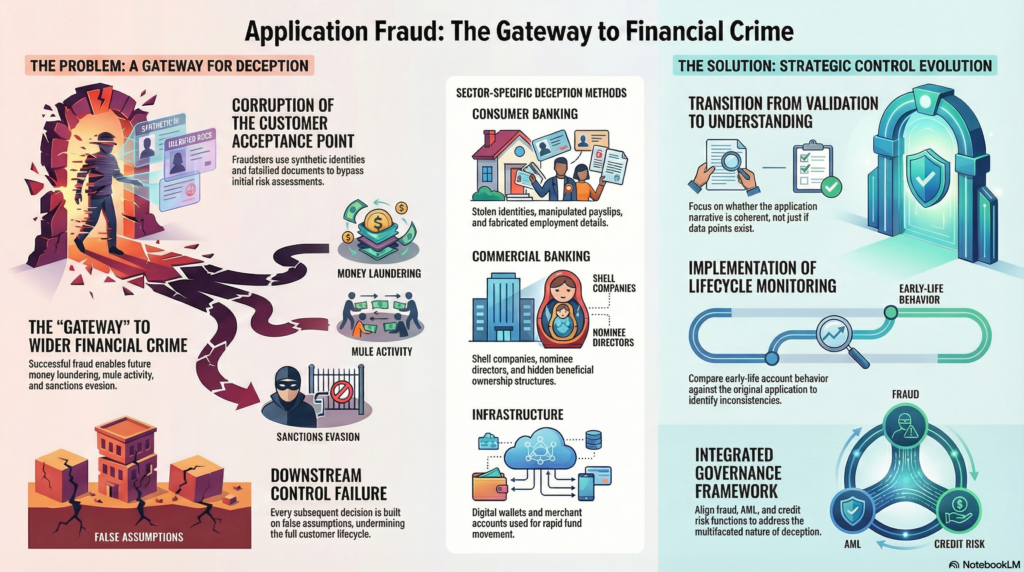
From a professional perspective, application fraud is best understood as an attack on customer acceptance integrity. Financial institutions rely on the application stage to determine who the customer is, whether the relationship is permissible, what risks are present, and what controls should apply. If that assessment is corrupted by deception, every downstream decision may be built on false assumptions. A customer may appear lower risk than they truly are, a business may seem commercially legitimate when it is not, or a product may be granted for a purpose entirely different from the one declared. This is why application fraud should not be treated as a narrow document-checking problem. It is a foundational control issue that can undermine the reliability of the full customer lifecycle.
The methods used in application fraud vary depending on the criminal objective. In consumer settings, the fraud may involve false personal details, manipulated payslips, fabricated employment information, misrepresented affordability, or the use of another person’s identity to obtain credit cards, loans, accounts, or other services. In commercial settings, the deception may be more complex, involving shell companies, nominee directors, falsified financial statements, hidden beneficial owners, or misleading descriptions of business activity. In some cases, the objective is immediate financial gain through credit or product access. In others, the purpose is to obtain account infrastructure that can later be used for mule activity, transaction laundering, sanctions evasion, or the movement of illicit funds.
This wider criminal utility is what makes application fraud especially important in the financial crime environment. A fraudulently obtained account, merchant relationship, or lending facility is not only a source of direct financial loss. It can become a criminal asset. Once opened, it may be used to receive fraud proceeds, disguise the source or destination of funds, support suspicious payment flows, create false commercial legitimacy, or establish transactional history that reduces suspicion. In this sense, application fraud often serves as the gateway through which broader criminal misuse becomes possible. The damage is therefore not limited to the moment of onboarding; it can continue throughout the life of the relationship.
Watch on YouTube: Application Fraud
One of the reasons application fraud is so difficult to manage is that it often appears credible at first sight. Documents may look genuine, identity details may match external records, and the application may fit an apparently ordinary customer profile. In digital and remote onboarding environments, institutions increasingly rely on uploaded evidence, automated checks, database matches, and workflow rules. That creates efficiency, but it also means criminals often only need to satisfy a threshold of plausibility rather than demonstrate true legitimacy. Where controls focus too heavily on verifying isolated data points instead of assessing the overall coherence of the application, fraud can pass through multiple checks without triggering meaningful challenge.
A critical professional distinction is the difference between validating information and understanding it. An address may exist, a company may be registered, and an identification document may pass technical verification, yet the application can still be deceptive in substance. The real question is whether the information makes sense when viewed as a whole. Does the declared employment align with the applicant’s profile and requested product? Does the business activity align with the geography, ownership structure, expected volumes, and transactional purpose? Does the source of funds explanation fit the nature of the relationship? Application fraud often succeeds where firms verify fragments of truth but fail to challenge the broader narrative.
The typology also overlaps heavily with other identity-related risks. Application fraud may involve direct identity theft, where a real person’s details are used without consent, or synthetic identity abuse, where genuine and fictitious details are combined to create a new customer profile. In some situations, the applicant is a real person misrepresenting key facts such as income, occupation, source of funds, or intended account use. In others, the application is submitted by an organized fraud network, intermediary, or complicit associate acting behind the scenes. These distinctions matter because they affect both the institution’s response and the wider financial crime implications. What may initially look like a simple false statement can in fact be part of a coordinated fraud, mule recruitment scheme, or laundering operation.
Application fraud is particularly significant where the product being obtained creates immediate transactional capability or deferred financial exposure. Current accounts, digital wallets, cards, merchant accounts, consumer loans, business banking services, and credit facilities are all attractive targets because they provide either access to value or infrastructure through which value can move. A criminal may build an apparently normal relationship before using it for suspicious payments or may seek rapid value extraction through credit drawdown or receipt of illicit transfers. This means application controls are not just about preventing onboarding losses. They are about preventing the creation of financial channels that can later be exploited for wider criminal purposes.
A mature control framework for application fraud begins with strong onboarding design. This includes robust identity verification, document validation, beneficial ownership review where relevant, corroboration of critical data, and escalation of inconsistencies that cannot be reasonably explained. But strong control design goes beyond validation. It requires contextual scrutiny. Firms need to ask whether the application is commercially, behaviourally, and operationally credible. Does the requested product make sense? Is the expected activity consistent with the customer type? Are there unusual contact points, shared devices, repeated addresses, or other linkages suggesting organized fraud? This level of scrutiny is where application fraud often becomes visible.
Detection after onboarding is equally important because not all fraudulent applications are identified at the point of submission. Some only become apparent through early-life account behaviour. Red flags may include immediate high-risk transactions, pass-through fund flows, unusual digital access patterns, rapid use of credit, discrepancies between declared purpose and actual usage, dormant-to-active account transitions, or transaction patterns inconsistent with the customer profile established during onboarding. These cases show why application fraud should be treated as a lifecycle risk rather than a one-time onboarding event. If the institution does not compare later account behaviour to the original application narrative, important warning signs may be missed.
The investigative dimension is also critical. Once suspected, application fraud requires more than a binary decision about whether the account should remain open. The institution needs to understand what the deception was intended to achieve. Was the purpose credit abuse, mule activity, suspicious payment processing, concealment of beneficial ownership, or access to financial infrastructure for future criminal use? This often requires review of linked applications, shared identifiers, device overlaps, associated entities, transaction patterns, and related accounts. A narrow case review may resolve the individual relationship while missing the broader network or typology risk.
Governance is essential because application fraud often sits across multiple control functions. It should be reflected in fraud risk assessments, customer acceptance frameworks, AML and sanctions onboarding controls, product governance, model performance reviews, and management information. Firms need to understand which products, channels, customer segments, and geographies are most exposed, and whether current onboarding standards reflect actual criminal methods rather than outdated assumptions. Metrics such as fraud rejection rates, early-life suspicious activity, post-onboarding remediation, document manipulation trends, linked-application clusters, and default rates associated with false information can help determine whether the control environment is effective.
There is also an important customer and reputational dimension. Where application fraud involves stolen identities, innocent individuals may suffer credit harm, denial of services, and significant remediation difficulty. At the same time, overly rigid controls can create unnecessary friction for genuine applicants and generate exclusion risk. A professionally mature framework therefore requires balance. Controls must be rigorous enough to identify deception, but proportionate enough to support fair access and consistent treatment of legitimate customers. That balance becomes especially important in digital-first environments, where speed and customer experience are commercially significant but weak onboarding controls can create long-term financial crime exposure.
Ultimately, application fraud is a core financial crime threat because it corrupts the point at which institutions decide who they are willing to trust. It allows criminals to obtain accounts, facilities, and products on a false basis, and once that access is granted, it can support fraud, credit abuse, mule activity, suspicious fund movement, and wider control evasion. In a modern financial services environment, effective application fraud management is not simply a matter of catching false documents. It requires institutions to assess the authenticity, coherence, and credibility of the full customer narrative, and to maintain that scrutiny throughout the life of the relationship. For that reason, application fraud should be treated as a strategic control risk requiring integrated onboarding standards, dynamic monitoring, strong investigative capability, and close coordination across fraud, AML, compliance, operations, and governance functions.




